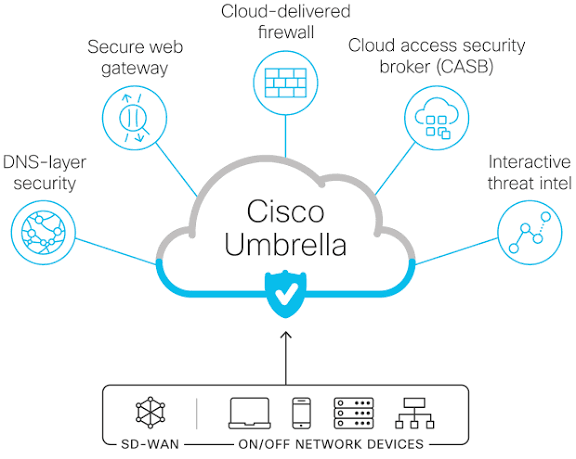
DNS Protection using Cisco Secure Client
Cisco secure client is a piece of software that install on a user pc, the endpoint. But it is not limited to, it installs also on mobile device. That’s just awesome! Let’s explore in this blog how this client helps secure the DNS. A little theoretical background Before we deep dive into how DNS protection…...