An anti-spam solution for my home network
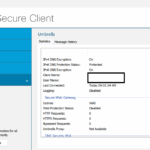
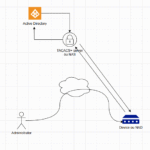
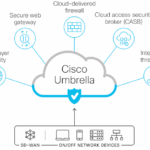
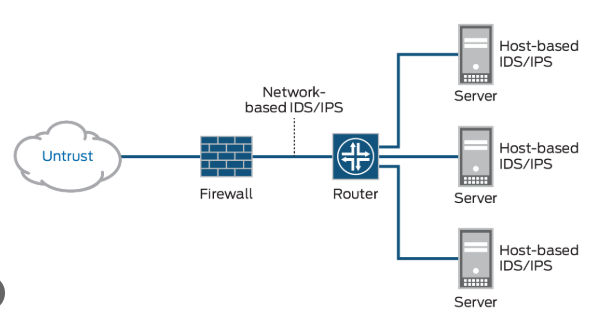
In this blog, let’s discuss the best way to secure my local mailbox. A little introduction Emailing application local or online come with multiple settings and options to secure emails exchange, and the content of the mailboxes. But many of them seem inefficient to block some of the spam traffic making the mailbox very hard…...