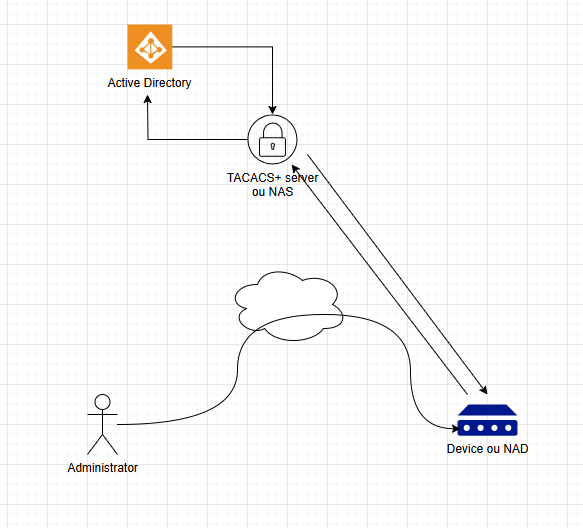
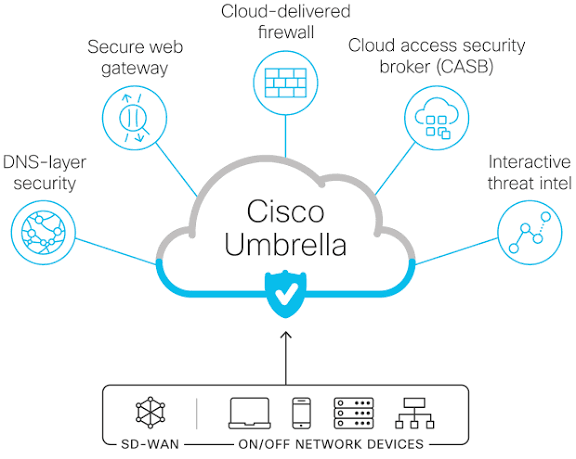
You have deployed your network which means installed, interconnected, configured and run your network devices. The connectivity between your users and servers is up and running. That a great news! but you’re worried about who may access locally or remotely to your network devices and eventually, change their configuration and operation… To secure this access…
TACACS+ for you Network