In this article we will discuss the use of WPA in a secured wifi context.
A little introduction
WPA stands for Wifi Portected Access. By protected access, the protocol define the way by which your device will authenticate to the wifi access point to be allowed to associate with this access point and futher, access to network resources that are behind this access point : wired network, lan, wan, datacenter, etc.
Let’s deep dive
No more WEP let’s move to WPA1
WEP stands for wired equivalent privacy and technically it means that the payload is encrypted following the RC4 algorithm. the receiver will de encrypt the packet for furter processing using the shared key and the initialization vector.
Here WPA1 enters into play, it enchances the previous procedure by using dynamic keys (TKIP) versus static keys (shared keys), and by including some message integrity check (or MIC). The MIC enhances the CRC checks already done by the WEP.
WPA1 is step towards WPA2
First of all WPA2 implements the mandatory elements of the IEEE 802.11i standard to achieve the CIA requirements: confidentiality, integrity and authentication. The network access in the new scheme is a multi-step process that can summarized as: fist secure the communication channel for key exchange, and after that, encrypt and send the data over.
First of all, the device associate to the access point. Then, it goes through a 4-way handshake (the AP sends an random number or ANonce, the client its SNonce, the AP calculate the PTK and encrypt, the client decrypt with the PTK and confirms successful auth.) to ensure both the device and the AP have the same pre-shard key (PSK) that is not transmitted over the air, instead a pairwise transient key (PTK or GTK if broadcat traffic) is generated and used for this purpose.
Second, after the securing the communication for key exchange, the procedure includes the use of AES/CCMP an advanced encryption standard using the counter-mode/cbc-mac protocol to ensure robust encryption and data integrity using different initialization vectors.
WPA3
WPA version 3 added more important features to strenthen to operation of the previous procedure, including: stronger 192-bit cyptographic encryption standard (AES-256 in GCM mode with SHA-384 as HMAC), more secure initial key exchange (SAE or 802.11s instead of PSK), no more TKIP, OWE or opportunistic wireless encryption for open wifi networks (that do not have passwords), protection of the management frames as in the dot11w.
WPA personal and enterprise modes
In the personal fashion of doing things a pre-shared (user) key is used to derive the other keys needed for the different phases of the communication securization.
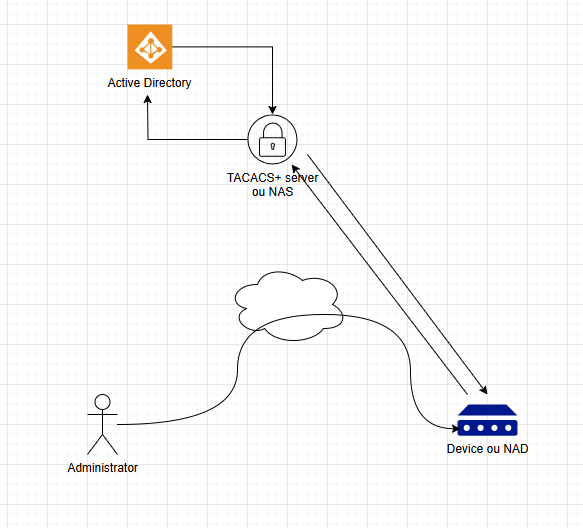
In the enterprise mode, with start using the dot1x stardard that dictates the use of a RADIUS service. The radius client (our access point for example) that is known to the radius server, authenticate the wifi users (devices, etc.) using one of the available EAP or extensible authentication protocol methods. Fuerthermore, the radius server, instead of using the local database, can interface with other systems such as a certificate authority, active directory, etc. to get the necessary information to authenticate the wifi clients.
Let’s summarize
WPA is the stardard today, the version 3 being the most secure in two modes: personal and enterprise. In enterprise mode, the use of RADIUS, dot1x and EAP, allow an enterprise-class even more secure network access.