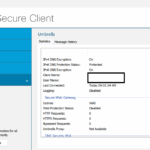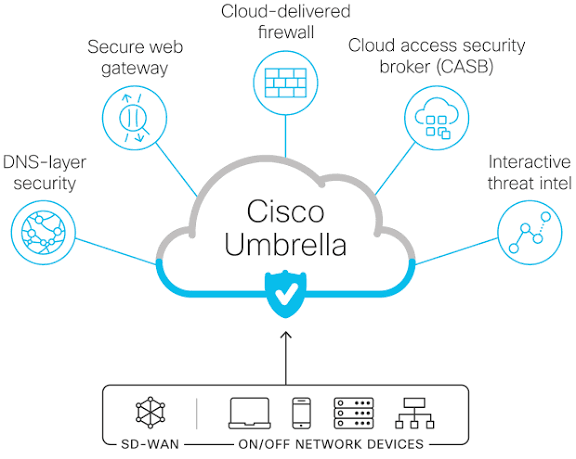
Cisco Secure Client and Agents
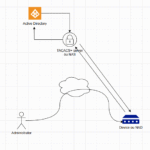
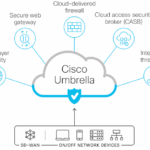
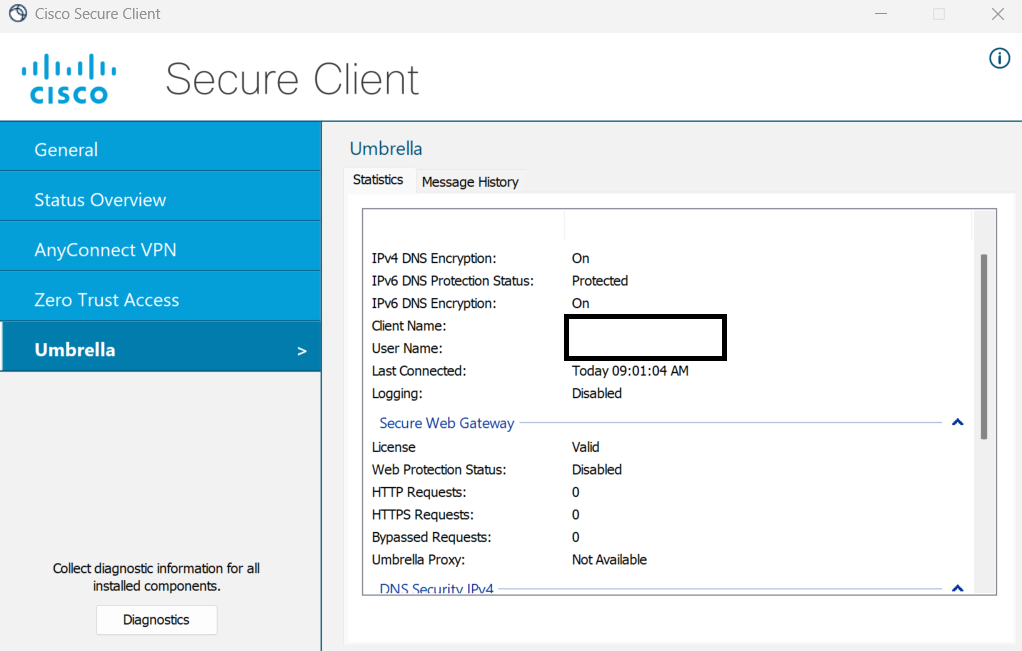
Cisco secure client helps secure access to the network at the endpoint level. it’s an endpoint security and embarks multiple agents (in one single client or piece of software). let’s detail the functionality of this client software. a bigger view the very usual use case is when a client tries to access enterprise resources. to…...